A year ago today …

A year ago today …
Here’s a gift for the Subway Surf fans out there: I’ve found a bug that will give you a never-ending magnet (at least until you’re caught).
The other night I was lying in bed playing Subway Surf (as you do) and was approaching a jetpack when I accidentlly swiped into a train, allowing the secuity guy to catch me up. As I was pickig up the jetpack I swiped into a train again, allowing the security guard to catch me. Except he stayed on the ground while my character flew into the air upside down as if being held up by one leg with magnet in hand. Capture avoided.
What was interesting though was that after the jetpack ran out my character dropped to the ground again and still had the coin magnet in hand even after the timer bar had run out. My curiosity got the better of me and I crashed into a barrier to se if I was invincible. I wasn’t but was a bit wealthier than I was when I started!
A colleague showed me an app the other day that helps produce crowd sourced mobile phone coverage and performance maps.
I’m sure everyone’s seen the mobile phone operators’ own coverage maps which are reasonably accurate but are based on maths rather than user experience and Rootmetrics have seen this as a gap that needs filling.
I have no idea how Rootmetrics make money but that’s their problem, not mine. The company has already mapped much of America and is now mapping the UK. Their employees have already driven round London and Hull testing the mobile networks and the gaps are being filled by mobile phone users like me who are running the continuous test on the Rootmetric app when travelling to build up coverage and performance data. The continuous test only works on the Android version of the app, not the iPhone version for some reason (probably a spurious “security” restriction imposed by Apple) and it’s pretty data hungry – the app has used over 750mb in 4 days – so you’ll only want to use it on an unlimited data plan.
The tests produced are a good guide for signal strength at least but the data stats are slightly less convincing which makes the Rootmetric score – a combined score based on signal strength and data speeds – a bit misleading. For instance, if I check my connection speed on the speedtest.net app I can get some blistering speeds for a 3G connection – 9.39mbit/sec one day this week – but the download speed is fairly average using Rootmetrics’ servers giving it a yellow/orange hexagon – which is more a refelection on Rootmetrics’ infrastructure than Three’s. I tether my tablet to my phone at work and at least one of my colleagues tethers to it in the office because he’s on Vodafone and they’re rubbish and it’s good enough to watch live TV on more than one device using the same connection.
That said, the idea of crowd sourcing mobile phone coverage data is a great one and I’m certainly doing my bit!
Orange/T-Mobile are launching a new 4G mobile phone service under the brand Everything Everywhere (EE), the name they gave themselves when the two networks merged.
 There’s been a bit of controversy around the 4G roll-out though. OFCOM, which is responsible for licensing the spectrum that 4G mobile networks will use, has given EE permission to use some of the spectrum it already owns to roll out 4G services ahead of the auction for the rest of the spectrum. Other mobile phone providers reckon this is a bit unfair as they don’t have any spare spectrum and EE only have spare spectrum because OFCOM gave them a big chunk for free a few years ago. They thought that was unfair at the time as well but nothing came of it.
There’s been a bit of controversy around the 4G roll-out though. OFCOM, which is responsible for licensing the spectrum that 4G mobile networks will use, has given EE permission to use some of the spectrum it already owns to roll out 4G services ahead of the auction for the rest of the spectrum. Other mobile phone providers reckon this is a bit unfair as they don’t have any spare spectrum and EE only have spare spectrum because OFCOM gave them a big chunk for free a few years ago. They thought that was unfair at the time as well but nothing came of it.
Three make a bit of a fuss about the way the 4G auction was going to be run, saying that it gave an unfair advantage to the big four networks who already had lots of spectrum. They have since done a deal with EE to run their own 4G services over their network. It’s a logical extension of the mast-sharing deal they currently have with Orange.
The 4G launch will be an Apple-free zone with only Windows 8 and Android phones expected in the first year and although Apple is rumoured to be preparing a 4G version of the iBrick it might not work with EE’s network.
It does seem a little unfair that EE are getting to launch their 4G network early but while it gives them an advantage at the outset being the only 4G provider, they’re going to find themselves running a network on the wrong frequency with a limited set of handsets as a result. They’ll buy more spectrum in the auction and then spend stupid money running the two alongside each other. This fragmentation happens in the US and it’s a nightmare – you get entire cities with only one operator because the mobile network has been built non-standard and no other operator’s handsets work.
Whatever happens, the rollout of 4G can only be a good thing. Fixed line broadband really has had its day – wireless has virtually limitless possibilities and can provide high speed data connections where laying miles of copper wires or fibre optics just aren’t an option. The only thing that is likely to hold it back is divergence as a result of EE’s early adoption and companies spending stupid money in the spectrum auctions and not having enough cash to invest in building the new networks.
Time for another geek interlude – tel: versus callto:
Taking WAP out of the equation because it’s so old as to be irrelevant, there are two ways to mark up telephone numbers in HTML. The tel: URI (Universal Resource Indicator – it tells your browser what it can expect to find at the destination of your link) is the official standard for marking up telephone numbers whilst callto: is a proprietary URI made popular by Skype and unsurprisingly, Microsoft.
By marking up a telephone number, it makes it easier for visitors to your website to make phone calls from their phones or computers – click on the link and it launches whichever application is set up to handle phone calls. But the problem is, which of the two do you accommodate on your website? Mobile devices are the obvious target because they’re usually going to be mobile phones so tel: would seem to be the obvious choice but it’s not uncommon for people to have Skype phones or another VoIP phone service so callto: support would be useful.
But you can’t have both so which should you use? Do you encourage standards compliance by using tel: or pander to the embrace and extend ethos of Sky and Microsoft and use callto:? Do you cater for mobile devices with tel: or desktops with callto:?
With the rapid convergence of internet and phones, we need some standards compliance in the major browsers. The last thing we need is a VHS/Betamax or Blueray/HD-DVD battle over telephone number markup standards!
 The British government’s ePetitions site has gone live today and failed spectacularly. Even this late in the day it’s still crashing more often than not as it’s not been scaled adequately for the feeding frenzy that was inevitable for its launch. Should have hosted it in a cloud with some other online services that have an annual peak later on in the year and used the latent capacity.
The British government’s ePetitions site has gone live today and failed spectacularly. Even this late in the day it’s still crashing more often than not as it’s not been scaled adequately for the feeding frenzy that was inevitable for its launch. Should have hosted it in a cloud with some other online services that have an annual peak later on in the year and used the latent capacity.
Sorry, should have posted a geek alert.
I’ve signed a few petitions tonight. Obviously I think they’re all important in one way or another otherwise I wouldn’t have signed them but these are my top three so please sign them too!
The reasons why we should have a referendum on membership of the EU are obvious. We’ve given away our sovereignty, our wealth and our resources to the EU. The sooner we’re out of it the better.
The reasons for an English Parliament are similarly obvious. It is a travesty that English still doesn’t have a government of its own and a national insult. England is the last colony of the British Empire, we need to throw off the British yoke and start running our own country for our own benefit.
Reinstating the hereditary peers is something I’ve written about several times. I have always believed it was a regressive step to abolish hereditary peers and the fact the the House of Lords is now full to bursting with politically appointed peers as reward for donations and services rendered backs that belief up. Only hereditary peers can give us the randomness and independence of though that is needed in government.
If any of these petitions reach 100,000 signatures then it will be debated in the House of Commons. 100,000 sounds like a lot but the road pricing petition started by Peter Roberts on the old Downing Street petitions website got almost a million signatures and according to the bods that ran that service, the petition did actually get well over 1m signatures but the site couldn’t cope with the demand and they weren’t all counted. 100,000 signatures is a lot for a petition but it’s not a number that can be dismissed easily.
Of course a debate doesn’t mean a change of policy and one MP (I forget who it was and where I read it) said that MPs should “lead on policy” not listen to what the people want. One thing’s for sure – if they don’t already want to change policy a 100,000 signature online petition certainly isn’t going to make them!

While I am a political animal nowadays, I am, first and foremost, a geek and I’ve been indulging my inner geek this last couple of weeks by installing Linux on a couple of laptops.
I haven’t played with Linux for about 7 or 8 years so I went for one of the most popular distros. It was going to be Ubuntu but it wouldn’t install on Mrs Sane’s laptop – a common problem with Ubuntu not liking the graphics card – so I plumped for OpenSuse instead and the KDE desktop.
The OpenSuse install went like a dream. The Partition Manager wasn’t the easiest to understand but that’s largely down to me not really thinking about what I was doing properly so I ended up only partitioning half the drive (note to self: remember to resize the partition on the laptop). The second install I did I did it properly – delete the Windows partitions, rescan the disk and go with the recommendations.
I encountered a couple of problems once I’d got OpenSuse and KDE installed which I’ll walk through below for the benefit of anyone else installing OpenSuse for the first time.
Changing your hostname
Figuring out how to change the hostname on KDE was the first thing that posed me a challenge but I found it eventually. The hostname is the name of your computer as it appears on the network and OpenSuse randomly generates one for you.
Here’s how to change it:
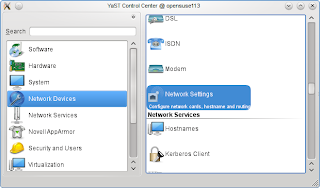
Click on the Application Launcher button (where the Start button is in Windows). Hover over the Computer icon at the bottom and then click on Yast. You will need to provide your root password for Yast. Select Network Devices on the left hand list and then Network Settings on the right. You’ll get a message saying that the network is controlled by NetworkManager – just click ok. Select the Hostname/DNS tab and put the new computer name in the Hostname box. If your computer is part of a domain, put the domain name here, otherwise whatever you enter will be the workgroup your computer is a member of. You may need to log off and back on again for the changes to take effect.
Installing Google Chrome
The other thing that gave me a headache was installing Google Chrome. This one wasn’t as easy to resolve as the hostname thing but I got it figured out in the end. If Google want to increase the take-up of Chrome on Linux then they really need to improve the installation process because it just doesn’t work on OpenSuse with KDE. Here’s how to do it:
 Go to http://www.google.com/chrome and download Chrome. Make sure you choose the correct installer – you want an rpm package. Once the package is downloaded, open a Terminal window. You need to be logged in as root to install Google Chrome so type in su – root, press enter and provide your root password. The installer package will be downloaded to /tmp so type in cd /tmp. Now you need to install the package – type in zypper – install google-chrome-stable_current_i386.rpm.
Go to http://www.google.com/chrome and download Chrome. Make sure you choose the correct installer – you want an rpm package. Once the package is downloaded, open a Terminal window. You need to be logged in as root to install Google Chrome so type in su – root, press enter and provide your root password. The installer package will be downloaded to /tmp so type in cd /tmp. Now you need to install the package – type in zypper – install google-chrome-stable_current_i386.rpm.
During the install you may be prompted for your root password and permission to install a number of packages – enter your password and agree to the other packages. Strangely, the installation package doesn’t actually install everything Google Chrome needs – without the png library, Chrome will load and then shut down without even displaying anything on the screen. To install the png library, you need to run zypper -install pnglib12-0.